Security Controls

My name is Valentina. but hey, just call me Vally, which means strength. I am the Powerhouse behind Cyvally. Vally is a rising cybersecurity professional and a content creator, I write to make cybersecurity and cloud topics understandable and interesting to you (after all, who likes boring?).
Action movie fans like myself will enjoy this: Marvel agents go on a quest to find a vital document locked within a safe in a building. The heroes were faced with series of difficulties, each emphasizing a different security control put in place by the Villian. The first obstacle is manipulating an electronic gate(Technical Control) of the building with sophisticated hacking tools to gain access. Next are wild guard dogs(Physical Control) which the team used their firearms on. When the team gets to the safe's room, they find a tripwire, a security device managed with strategic precision. Contact with this wire will instantly sound an alert; this feature is managed by managerial control. Operational control is demonstrated by the last barrier of security, an identification mechanism at the impenetrable safe where fingerprint scans, retinal recognition, and voice authentication become the key to unlocking the safe
In this post, you will learn about the different types of security controls
WALK WITH ME!!!
WHAT ARE SECURITY CONTROLS
I appreciate the NIST definition of security controls, which states, "A countermeasure prescribed for an information system or an organization, designed to protect the confidentiality, integrity, and availability of its information and to meet a set of defined security requirements." This definition highlights that we not only need security controls to ensure the CIA of information but to also align security measures or countermeasures with specific objectives and standards set forth for information protection.
HAVEN'T HEARD ABOUT CIA TRIAD?
CYVALLY GAT YOU WHAT IS CIA?
CATEGORIES OF SECURITY CONTROLS
- Technical: refer to the use of technology for risk management and reduction
Examples include antivirus software, intrusion detection systems, access controls, encryption, and firewalls.
- Managerial: Often referred to as administrative controls, concentrate on planning, policies, and procedures to manage security risk.
Examples are incident response plans, security awareness training, risk assessments, and security policies.
- Operational: includes day to day procedures and actions that enhance security.
Examples include incident reporting, change management, backup processes, and user authentication.
- Physical: are measures that prevent unauthorized physical access to assets.
Examples include locks, security cameras, biometric access controls, and environmental controls (such as fire suppression systems).
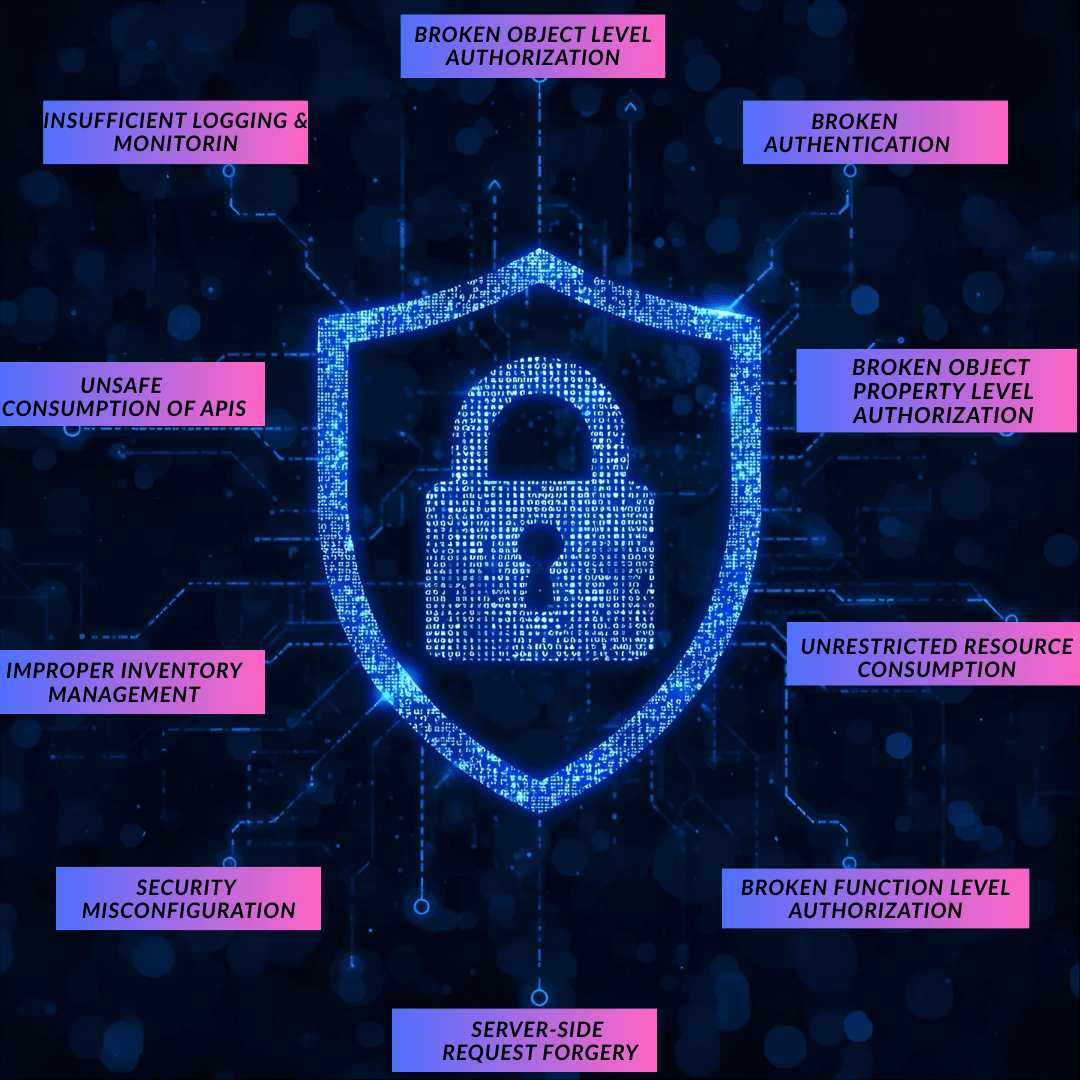
TYPES OF SECURITY CONTROLS
Preventive: measures to stop security incidents before they happen. Examples are access controls, encryption, IPS and firewalls.
Deterrent: measures to discourage potential attackers making their effort less tempting to continue. Examples include noticeable surveillance cameras, security patrols, and warning signs.
Detective: measures to identify and alert as security incident happens. Examples include log monitoring, security audits, and IDS.
Corrective: measures to mitigate the impact of security incidents and return systems to normal operation. examples are recovery techniques, system backups, and incident response plans.
Compensating: measures that offer substitute protections. Multi-factor authentication is an example.
Directive: Guide behavior and actions to ensure compliance with security policies. Examples include awareness and training programs, safety policies and procedures.
To provide a multi-layered defense against a range of threats, it is frequently necessary to combine several control types and categories for better effectiveness.
“Technology trust is a good thing, but control is a better one.”
Stephane Nappo
REVIEW QUESTIONS