What is API Security?
My name is Valentina. but hey, just call me Vally, which means strength. I am the Powerhouse behind Cyvally. Vally is a rising cybersecurity professional and a content creator, I write to make cybersecurity and cloud topics understandable and interesting to you (after all, who likes boring?).
I recently discovered that generations before Gen Y had their own official names, too. For the longest time, I assumed the naming trend began with Gen Y, the Millennials, then continued with Gen Z, and now Gen Alpha. But like everything else in history, people had been labeling generations long before the digital age.
What interests me, though, is how differently each group relates to technology. Millennials are widely seen as the generation that adapted to technology. Gen Z grew up with technology as a constant, almost like a second language. And Gen Alpha? They are growing up fully immersed in a world where AI, touchscreens, and digital ecosystems aren’t innovations; they’re just the normal way life works.
But today's discussion is really about Gen Z.
The first time I heard Vandana Verma Sehgal say, “APIs are like Gen Z,” it stopped me. Immediately, my mind went to all the bold, unfiltered, and sometimes hilarious comments employers make about Gen Z on Twitter. You know the ones, calling them audacious, direct, uncompromising, and allergic to nonsense.
But the moment she explained her analogy, it made perfect sense. APIs and Gen Z genuinely share more similarities than you would expect. They’re fast. They’re expressive. They expect clarity. They don’t like ambiguity. And they absolutely will not tolerate friction.
And just like Gen Z, APIs never hide; they communicate openly through clear responses, detailed errors, and transparent documentation. Everything is meant to be visible and discoverable. Yet in the same breath, APIs can overshare too, exposing more data than intended, revealing internal details, or exposing sensitive information when not properly secured, exactly the way people joke about Gen Z oversharing their thoughts and lives online.
The comparison was so accurate that I couldn’t help but laugh and agree. There isn’t much difference between these two super forces.
And that’s exactly what I’m about to show you.
In this blog post, we’ll explore the fundamentals of API security, what it is, why it matters, and the essential best practices every developer, business, and security professional must apply to protect data and system integrity and stay secure in an increasingly API-driven world.
APIs and API Security: What They Are and Why They Matter
What is an API?
API is an acronym for Application Programming Interface. Let’s break it down:
An application is a software program that performs a specified function.
Programming is the process of writing instructions that tell software how to work.
Interfaces are agreements that define how two applications communicate.
Putting it together, an API is a software intermediary that allows different applications, services, systems, and databases to communicate and exchange data efficiently.
What is API Security?
API security is the process of protecting APIs’ integrity from attacks, data breaches, unauthorized access, and other security risks. It addresses techniques, methods, measures, best practices, protocols, and solutions for detecting, understanding, and mitigating the unique vulnerabilities and risks associated with both your APIs and the third-party APIs you rely on.
Why API Security Matters
APIs are the heart that makes modern applications operate. They power web apps, mobile apps, cloud services, and the connections between systems. Insecure APIs can result in severe consequences, including:
Data breaches and exposure of sensitive information.
Unauthorized access to critical systems
Service disruptions and financial loss
Reputational damage
In short, API security is important because APIs handle sensitive data and critical functions in modern apps. Protecting them helps organizations maintain trust, compliance, and operational integrity.
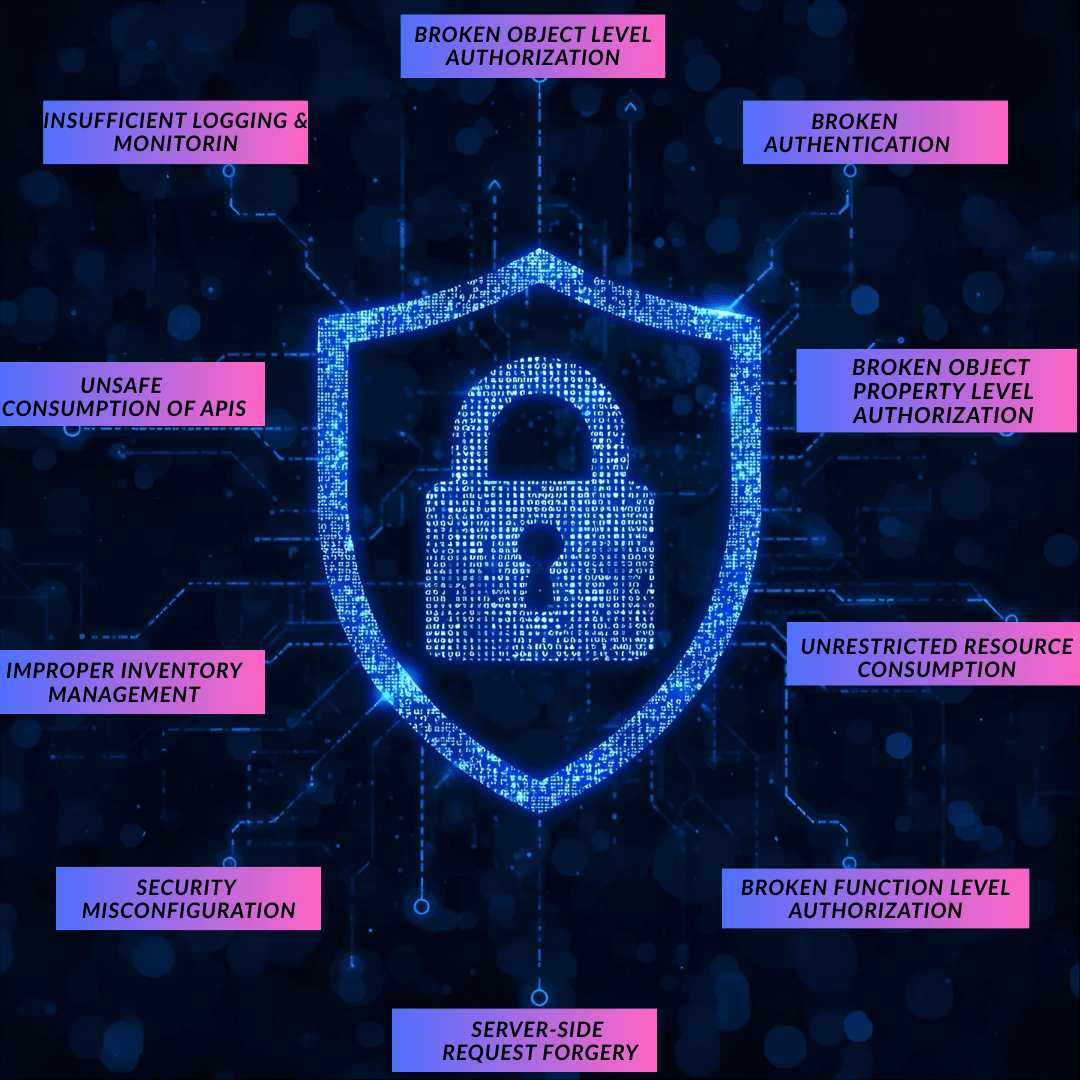
OWASP API Security Top 10
001: Broken Object Level Authorization(BOLA)
What it is: An authorization flaw vulnerability occurs when an API permits a user to access the data of another user without adequately verifying if the user is allowed to do so.
How to prevent it: Always enforce and continuously test authorization controls across all endpoints, and verify users have permission to access or alter objects before processing requests.
002: Broken authentication
What it is: This vulnerability arises from a poor or improperly implemented API authentication method. This gives attackers an opportunity to take control of user accounts, access their sensitive data, or carry out actions on their behalf.
How to prevent it: Implement strong authentication mechanisms, such as multi-factor authentication (MFA).
003: Broken Object Property Level Authorization
What it is: This vulnerability happens when an API fails to implement proper access control for particular elements of an object, resulting in the disclosure or manipulation of sensitive data. The issue stems from two flaws: mass assignment (when APIs modify object properties without verifying user authorization) and excessive data exposure.
cUse allow lists (whitelists) for fields so that users can only modify specific, permitted properties. Apply data minimization to return only the minimum amount of information.
004: Unrestricted Resource Consumption
What it is: This vulnerability exists when an API permits users to consume excessive amounts of system resources (CPU, memory, and bandwidth) without any restrictions. It can result in slow performance, system crashing, and to initiation of denial-of-service (DoS) attacks
How to prevent it: How to Avoid It: Implement rate limiting to restrict the number of requests that an IP or user can make in a particular period of time. Monitor API performance to detect anomalous consumption spikes.
005: Broken function-level authorization
What it is: The API lacks proper authorization checks at the function or operation level, allowing users to access authorized functionality. Authorization issues are commonly created by complex access control policies and ambiguous responsibilities, allowing attackers to access resources and administrative powers of other users.
How to prevent it: Implement role-based access control and test all endpoints to identify any permission gaps or unauthorized access.
006: Unrestricted Access to Sensitive Business Flows
What it is: This vulnerability arises when attackers study the business model of an API, identify key business flows, and automate access to them, which could be destructive to the business at large.
How to prevent it: Think like an attacker when identifying threats, and implement authorization rules to limit the creation of resources.
007:Server Side Request Forgery (SSRF)
What it is: This vulnerability occurs when an API accepts a link from a user without validating it. When the server tries to navigate to this link, it forces it to visit endpoints it should not, potentially allowing access to internal systems.
How to prevent it: Validate and sanitize all input, and implement network segmentation and firewall rules
008: Security Misconfiguration
What it is: This vulnerability occurs when a system, application, or network is not configured securely. Incorrect or flawed security settings might reveal gaps that attackers can exploit.
How to prevent it: Regularly audit your systems to find misconfigurations and vulnerabilities, and keep all software patched and updated to fix security issues.
009: Improper Inventory Management
What it is: You can't protect APIs you don't know exist. Without effective tracking, some APIs may exist without your team's knowledge; they are known as zombie or shadow APIs.
How to prevent it: Because APIs typically have a large number of endpoints, keep up-to-date documentation and an inventory of them. Manual tracking can be burdensome, so adopt automated tools to maintain and secure hidden APIs. Make API documentation visible only to authorized users.
010: Unsafe Consumption of APIs
What it is: This vulnerability exists when you use third-party APIs that you simply do not fully control. Even if your own API is secure, relying on external APIs might be risky since attackers may target the connected services.
How to prevent it: To eliminate security risks, maintain an inventory of all third-party APIs, encrypt all communications, validate all supplied data, and enable error handling.