Sec+ #003: Application Attack Indicators
My name is Valentina. but hey, just call me Vally, which means strength. I am the Powerhouse behind Cyvally. Vally is a rising cybersecurity professional and a content creator, I write to make cybersecurity and cloud topics understandable and interesting to you (after all, who likes boring?).
Dear Cyvally Readers,
I am sure you are expecting a storyline to begin introducing the different types of application attacks. However, I decided to spice things up today by providing us with a short scenario to explain each application attack. I have heard a lot of people complaining that this objective of the CompTIA sec+ is boring and they find it challenging, so I'm hoping this method will help to make the concepts clearer, relatable, and easily understandable. also, I will appreciate your feedback, as it will assist me in updating the content depending on your comment and suggestions. On this note, make sure to return to each post to ensure you are up to date with the latest info. I appreciate your continued support.
CYVALLY READERS ARE THE BEST!!!
Stay in the loop!!!
As a Cybersecurity Professional, you will frequently encounter the term threat actors, who use code execution attacks to break into networks on hosts, resulting in major issues such as data asset breaches, denial of service attacks, and exploitation of privileges and access. YOU DON'T WANT THESE ISSUES, DO YOU?
HEARD ABOUT ARBITRARY CODE EXECUTION AND REMOTE CODE EXECUTION?
you can deduce each word from its name; the word arbitrary means "random." ACE indicates a threat actor exploiting a vulnerability and executing random code on the target system. RCE indicates an attacker executing code on a remote target.
In this post, you will learn about application attack indicators to help identify present or future attacks on applications. By thoroughly investigating these indicators, you and I will be able to detect and respond to application attacks SOMEDAY. I HOPE YOU'RE EXCITED, AS I AM.
#1: Privilege escalation
The term "escalation" refers to the process of making something bigger or more serious. Privilege escalation occurs when an attacker upgrades their access level from user to administrator/root, they get greater control over a system, network, or application.
SCENARIO: Assume Harry, an attacker carried out a phishing attack (I ASSUME YOU UNDERSTAND WHAT A PHISHING ATTACK IS) that allowed him to obtain unauthorized access to ABC's company network. Beginning as a regular user, he discovers and exploits a weakness in the system that allows him to increase his privileges as he gains access to the admin account( OUCH!!!, YOU PROBABLY KNOW THE END TO THIS STORY
There are two types of privilege escalation attacks, vertical and horizontal. Vertical occurs when an attacker attempts to elevate their privileges to a higher level than their initial access while horizontal occurs when an attacker aims to attain the same level of privileges as initial account.
Mitigation
- Implement strong access controls and least privilege principles
- Update anti-virus/anti-malware software to block known vulnerabilities
- Employ defense-in-depth strategies to limit the impact of successful attacks.
- Perform regular software patching, monitoring and auditing of user activities
#2: Cross-site scripting
Cross-Site Scripting (XSS) is a web security vulnerability where attackers inject malicious scripts into web pages. This occurs due to weak user input validation. When a victim visits the compromised page, the injected script executes in their browser, allowing attackers to steal data or perform unauthorized actions.
Scenario: In an online forum, an attacker named Linda identifies a vulnerability in the comment section. Exploiting this vulnerability, Linda injects malicious code, such as <script>alert('XSS')</script>, into the search field. When the user clicks on the "enter" button, the injected script executes, potentially causing harm or displaying unwanted content.
TIP: Notice <script> was used to indicate it is a XSS code
There are 3 types of XSS attacks;
Reflected/non-persistent XSS: occurs when the malicious script is provided over the web server without being stored or persistent.(it is due to server-side flaw)
Persistent XSS: when website's database stores the script permanently.(due to server-side flaw)
DOM-based XSS: occurs due to flaw in the client-side code.
Mitigation
- Implement input validation, output encoding and content security policies.
- Mitigation measures such as limiting types & sizes of file uploads and whitelisting inputs.
- Use a well-designed anti-XSS input library functions
- Regularly perform Vulnerability testing for XSS vulnerabilities for every application.
#3: Injections Types
Structured query language (SQL): is a vulnerability that allows an attacker to tamper with database queries made by an application. It allows an attacker to the read and modify sensitive data from the database(Insert/Update/Delete). Proper input validation, parameterized queries, and regular software updates are required to prevent SQL Injection.
' or 1=1--
The string ' or 1=1-- is a common SQL Injection payload. It can be used to bypass authentication by manipulating the SQL query executed by the application. The 1=1 condition is always true, allowing unauthorized access to the system or retrieval of sensitive information from the database.
DLL Injection: A Dynamic-Link Library is a Windows library that allows sharing of code with other programs to perform specific tasks. DLL injection is a vulnerability where arbitrary code is executed into another process's address space by forcing it to load a foreign DLL. keep antivirus software up-to-date to prevent DLL Injection.
Lightweight Directory Access Protocol Injection: is an application attack that targets web-based applications by manipulating LDAP statements, usually generated from user input. LDAP is used for reading and writing network directory databases. An attacker can exploit either unauthenticated access or vulnerabilities in a client application to inject arbitrary LDAP queries. This can lead to unauthorized activities such as creating or deleting accounts, as well as modifying authorizations and privileges. Proper input validation and encoding prevents LDAP Injection.
Extensible Markup Language Injection: XML is a markup language that allows you to define any data with rules. XML Injection is a type of attack that manipulates or compromises the logic of an XML application or service. Proper input validation prevents XML Injection.
#4: Pointer/object dereference
Pointer dereference is a vulnerability that occurs when code attempts to access memory through a pointer, but the pointer itself is null or points to an invalid memory location. Pointers in languages like C/C++ store memory addresses, and dereferencing a pointer involves reading from or writing to the memory location it points to.
Scenario: An attacker named Nick took advantage of a weakness in a banking application to exploit a null pointer assignment. Nick causes a null pointer dereference error during account retrieval by giving a null value as the account pointer, resulting in a bank service crash and Nick gaining unauthorized access to sensitive data.
Mitigation
- Programmers should include logic statements that ensure that a pointer is not null before using it.
#5: Directory Traversal Attack
A directory traversal attack occurs when an attacker gains access to files or folders outside the intended scope of an application. This attack exploits the improper handling of user input used to construct file paths or directory references. By manipulating the input, the attacker can deceive the application into accessing unauthorized files or folders.
Scenario: For instance, a certain application allows users to download files by providing the file name in the URL, an attacker inserts "../" sequences to access files beyond the app's designated download folder and browse through the directory tree(INSERT HEARTBREAK EMOJI) this led to disclosure of confidential data, unauthorized access, or even remote code execution.
Mitigation
- Implement proper input validation and sanitization
- Implement secure coding practices and employ web application firewalls
#6: Buffer overflows
A buffer overflow occurs when data surpasses the capacity of a target buffer, causing damage to adjacent memory. This can lead to system crashes or enable attackers to execute unauthorized code. During a buffer overflow attack, the attacker intentionally sends data that exceeds the intended capacity of the buffer.
Scenario: For example, a program that expects a maximum of 15 characters for a username but receives a string of 100 characters can experience a buffer overflow if not handled correctly.
Mitigation
- Perform bounds checking by Implementing correct input length validation, for example, by using safe library functions for inputs.
Note: Bounds checking is a programming security approach that validates and enforces the right boundaries of arrays or buffers.
#7: Race conditions
A race condition is a vulnerability that occurs when the outcome of a program depends on the sequence and timing of events. It refers to the situation where multiple operations are performed at same time. Race conditions can be found in distributed or multithreaded programs.
Scenario: Jossy and Presh are both attempting to book the last remaining seat for an Infosec.Live event. Before booking the seat, each checks the value of "availableSeats" to ensure there is still a seat available. However, due to a race condition, both Jossy and Presh read the value of "availableSeats" simultaneously and mistakenly determine that there is still one seat available. Consequently, both proceed to book the seat at the same time.
Time of check/time of use: is a vulnerability that arises when there is a time gap between when a resource is checked and when it is actually used, allowing for potential modifications or compromises to occur during that interval.
Mitigation
- Design data structures or objects to be immutable, which means they cannot be updated after being created.
- Use thread synchronization where a part of the program can only execute one thread at a time
- Incorporate time stamp verification techniques to validate the consistency and integrity of resources.
#8: Improper Error handling
Errors are inevitable in every application and so should be handling properly. Attackers can exploit error management procedures to gain access to sensitive data by intentionally triggering errors.
Scenario: An attacker exploits a weakness in the authentication process by submitting a specifically designed username that causes an error. This forces the application to display a generic error message, revealing the existence of the username in the system. Although the password is incorrect, this information allows the attacker to launch further attacks, such as password brute-forcing.
Mitigation
- Record error details in a secure log file that is protected by access control
- Avoid echoing error information to users
- Error messages shouldn't divulge configuration or platform information that could help attackers, like disclosing database server information on an error page for a web application.
#9: Improper input handling
Attackers often exploit insufficient input validation by sending malicious data to vulnerable processes. This can result in various security vulnerabilities such as SQL injections, buffer overflows, and denial of service attacks.
Scenario: An attacker named Alex uses SQL injection to modify the database of an online shopping application with a flawed search feature. By inputting a devised search query, the application executes it without adequate validation, allowing the injected SQL code to run. Alex can then use the poor input processing vulnerability to access sensitive data, change prices, or remove the entire product catalog.
Mitigation
- Implement strong input validation procedures that verify the desired input data's format, type, and length. such as input sanitization, whitelisting, and blacklisting
- Perform Regular software updates and patching
- Regular security testing, including code reviews and penetration testing, should be carried out in order to identify and fix any possible vulnerabilities in the input handling logic.
#10: Replay attack
Replay attack involves intercepting and reusing authentication data to establish a session. The goal of replay attacks is to recreate the conditions of a previous event. If an attacker can record a series of packets, they can easily replay them, potentially making previously legitimate actions valid again.
Scenario: an attacker captures and records a user's payment transaction, and then replays it multiple times. This deceives the system into processing duplicate payments, allowing the attacker to gain unauthorized benefits.
Session replays: When a user establishes a web connection to a system, the connection creates a "session" in the sense that the different data sent back and forth create an interaction between the client and the server. The recreation of this interaction after it has already taken place is known as a session replay.
Scenerio: a legitimate user, Baron, securely logs into an online banking application and performs transactions. Meanwhile, a malicious attacker named Adam captures the session data, including the session identifier and authentication token. Even after Baron logs out, Adam replays the captured session data to the banking application's server. The server, unaware of the replayed session, validates the data and grants unauthorized access to Baron's account.
Mitigation
- Implement appropriate security measures such as secure cookie handling, strong session management
- Use Secure Communication Channels
- Implement timestamps or nonce (unique numbers or strings) in the authentication process.
- Use session tokens or tokens with one-time use to authenticate and authorize users.
#11: Integer overflow
Integers (whole numbers) are data types defined with fixed lower and upper bounds. An integer overflow attack occurs when a computed result is too large to fit in the allocated storage space, resulting in a crash or data corruption, as well as a buffer overflow.
Scenario: For Instance, positive number becoming negative such as transferring money from one account (the debit account) to another account (the credit account)(NO WONDER WE HATE DEBIT ALERT)
Mitigation
- Implement proper input validation and perform appropriate checks to prevent integer overflow vulnerabilities.
#12: Request Forgeries Types
Server-side request forgery (SSRF): SSRF occurs when an attacker manipulates a server-side application to send HTTP requests to a domain chosen by the attacker. This attack exploits the trust relationship between the server and the target, leading the vulnerable application to perform unauthorized actions. SSRF commonly targets the server itself or other back-end systems within the organizations
Cross-site request forgery (XSRF): CSRF occurs when an attacker manipulates a user's browser to execute undesirable actions on another website without the user's knowledge or consent. This is accomplished by taking advantage of the trust that websites have in the user's browser.
Scenario: In a CSRF attack, an attacker can exploit a bank's lack of authentication checks for each transaction. If a user is logged in and their browser remains open, the attacker can send a hidden request from another tab, making it appear as if the user initiated the transaction when, in reality, they did not. This allows the attacker to perform unauthorized financial activities on the user's behalf.
Mitigation
- Limiting authentication times and managing cookie expiration
- Testing for CSRF attacks should be part of the design process.
- checking the origin of requests and enforcing strict access control measures.
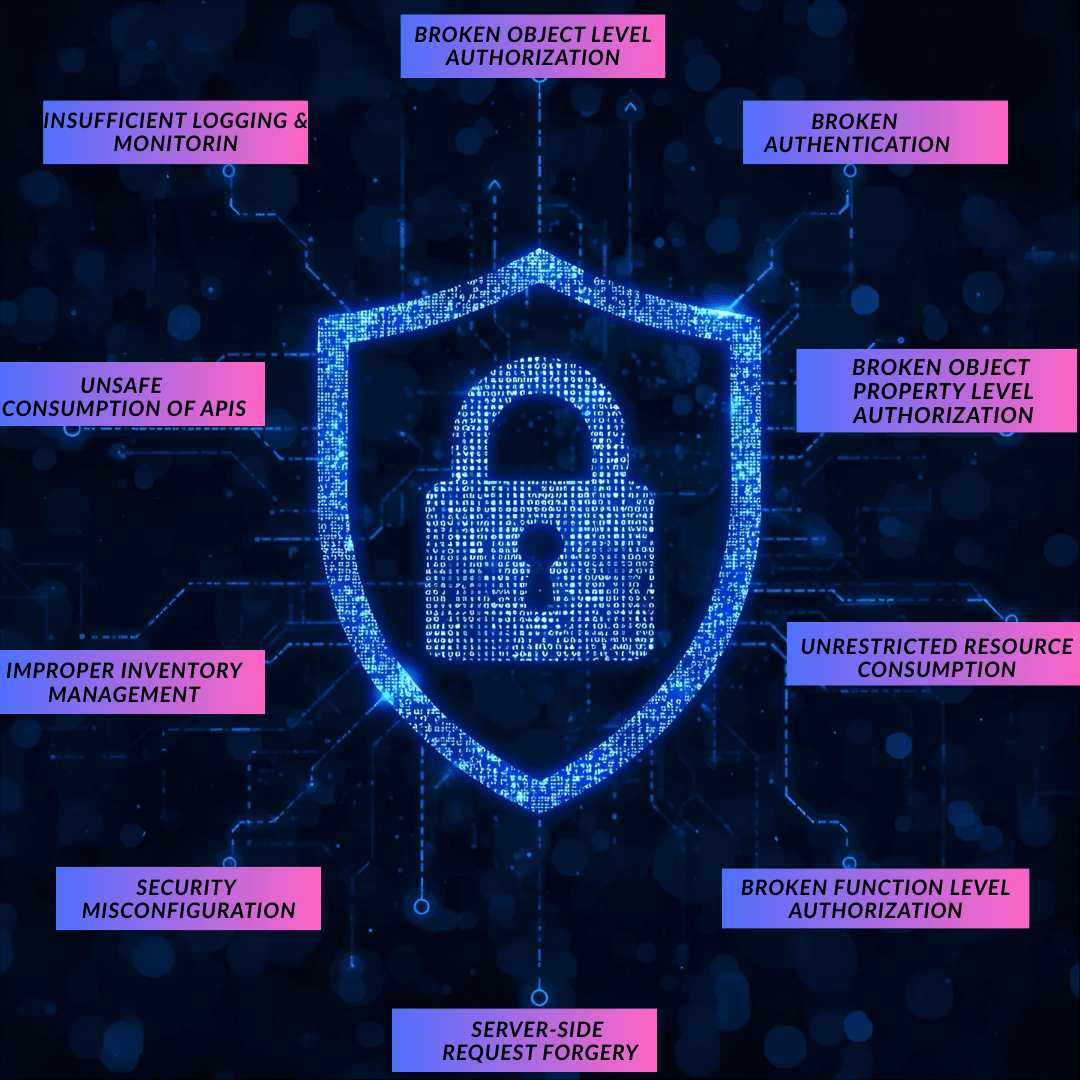
#13: Application programming interface (API) attacks
APIs are used to provide/feed data to an application. They are commonly used in web apps and cloud services to enable consumers to automate tasks. If an API is not secure, threat actors can easily exploit it to compromise the web application's services and data. Therefore, it is critical to ensure that the API is accessed exclusively through an encrypted channel (HTTPS).
Scenario: An online shopping platform has an insecure API endpoint for fetching product details. An attacker named Mike exploits this vulnerability by sending unauthorized requests to the API. Using a script, Mike retrieves sensitive information, including product prices, customer reviews, and inventory status.
Mitigation
- Use HTTPS and TLS/SSL certificates for secure communication.
- Implement input validation and sanitization to ensure only safe data is accepted.
- Employ strong authentication mechanisms like secure tokens or OAuth.
- Store and manage API keys and sensitive information securely.
- Implement proper error handling and message obfuscation to protect sensitive data.
- Apply rate-limiting and throttling to prevent excessive API requests and potential DoS attacks.
#14: Resource exhaustion
Resource exhaustion happens when a system lacks sufficient resources like capacity and memory, leading to system crashes and service disruption. Attackers exploit this vulnerability to deplete resources, causing system overload.
Scenerio: by overwhelming a system with TCP SYN requests or exhausting program memory which affect customer-facing systems and essential services. They target CPU time, memory, disk capacity, and network utilization, rendering systems unresponsive or filling up state tables.
Mitigation
- Implement measures such as resource monitoring, limitation, load balancing, rate limiting, intelligent resource allocation, secure coding practices, and attack detection and response
#15: Memory leak
Memory management is the process of controlling and coordinating computer memory, allocating it to variables, and reclaiming it when it is no longer required. Memory leaks occur when allocated memory is not released once it is no longer in use. This can result in increased resource usage over time, potentially causing system instability.
Scenario: A web-based app allows users to upload photographs, but a code issue prevents the allotted memory from being released once the images have been processed and stored. Memory accumulates without being released as users submit more photographs, resulting in a memory leak. As memory utilization increases, the application's resources are depleted, resulting in system instability or crashes.
Mitigation
- Implement proper resource deallocation
- Utilize automated memory management mechanisms
- Conduct code reviews and testing.
#16 : Secure Sockets Layer (SSL) stripping(HTTP downgrade)
SSL stripping is a man-in-the-middle attack against all SSL and early versions of TLS connections where an attacker downgrades a secure HTTPS connection to an insecure HTTP connection. By intercepting the traffic, the attacker can manipulate and read or modify the transmitted data. The reason the attack works is because the beginning of an SSL or TLS (v1.0 or v1.1) handshake is vulnerable to attack.
Mitigation
- Only use TLS 1.2 or 1.3 version
- Enforce HTTPS connections
- Educate users about secure connections
#17: Driver manipulation
Drivers act as a bridge between the operating system and peripheral devices. Drivers may have less protection compared to other core system components but are still integral to its functioning.
Shimming: A shim is an additional code that is placed between an application driver and the operating system to enable functionality that would otherwise be unavailable. It allows modifications between different OS versions without altering the original driver code, giving it flexibility and portability. Shimming can be exploited by malicious code to change the functionality of a driver without altering the driver itself.
Refactoring: the practice of restructuring application code in order to improve its design and performance while retaining its original functionality. It can be used to improve code or to deal with certain scenarios. However, attackers can use refactoring to introduce illegal functionality to a driver while still allowing it to work normally. it is a Metamorphic malware that can appear different each time
#18: Pass The Hash
This is an attack in which the attacker takes hashed user credentials and uses them to authenticate on the same network or other systems without knowing the original password. This technique makes use of hashed passwords rather than plaintext passwords for authentication.
Mitigation
- Enforce strong password policies and implement the principle of least privilege
- Implement network segmentation to isolate critical systems.
- Minimize credential exposure and use centralized authentication.
- Use multi-factor authentication (MFA) for an additional layer of security.
- Implement privileged access management (PAM) solutions for secure management of privileged accounts.
- Provide regular security awareness training to educate users and administrators.
- Keep systems and software up to date with the latest patches.
- Monitor for suspicious activities and use security tools for detection.
Time is what determines security. With enough time nothing is unhackable.
Aniekee Tochukwu Ezekiel
Review Questions