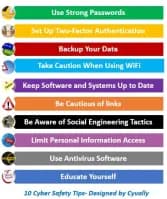
Cybersec base #007: Cyber Safety Tips
My name is Valentina. but hey, just call me Vally, which means strength. I am the Powerhouse behind Cyvally. Vally is a rising cybersecurity professional and a content creator, I write to make cybersecurity and cloud topics understandable and interesting to you (after all, who likes boring?).
Ken got an email from a company pretending to be his bank, requesting that he update his account information. Ken clicked on the link in the email without verifying the sender or the website URL and inputted his account information. He later discovered it was a phishing email, and the cybercriminals had depleted his bank account. Ken discovered the significance of cybersecurity and the importance of always verifying the sender and the URL before entering any private information online.
DONT BE A "KEN"
In this post, we will discuss 10 simple cyber safety tips to help you keep your personal information safe. Remember to share these tips with your employees and loved ones.
HOLD ON TIGHT FOR THIS RIDE!!!
TIP #1- Use Strong Passwords
Passwords are one of the most vulnerable points in the Internet security hierarchy. When generating a new password, keep strong password requirements in mind:
Use at least 12 characters, but 14 or more is preferable.
A mix of capital and lowercase characters, numbers, and symbols.
Do not use a dictionary word, name of a person, character, product, or organization.
Use passwords that are different from your previous ones.
Use something distinctive that is easy for you to remember but tough for others to guess.
Ensure that you frequently change your passwords.
Never reveal your passwords to anyone, have ZERO TRUST
Ensure that passwords and password hints are securely saved.
Use different emails and passwords for different accounts
Avoid using personal information in your passwords
TIP #2- Set Up Two-Factor Authentication
Two-factor authentication stops hackers from gaining access to your accounts and personal data. It Increases your account security by adding this extra layer of protection, even if someone knows your password.
Consider utilizing an authenticator app, such as Microsoft Authenticator, to create unique time-based codes for authentication.
Enable Two-Factor Authentication on All Your Accounts.
Keep your authentication device, such as your phone or authenticator app, secure
Once you've configured two-factor authentication, ensure sure it's operating properly. Log out of your account and then log back in using your authentication method to confirm that everything is working as it should.
TIP #3- Backup Your Data
Back up your data on a regular basis to avoid data loss in the event of a security breach or ransomware attack
Automate your backup process to ensure that your data is backed up on a regular basis without the need for manual intervention.
Select a secure backup location that is independent from your primary device, such as an external hard drive or a cloud storage service with robust encryption.
Make sure your backups are working properly by testing and confirming them on a regular basis. YOU DONT WANT TO BE CAUGHT UNAWARE
Consider backing up your data in multiple locations for redundancy and security against data loss.
Identify and prioritize the most crucial data that needs to be backed up, and make sure you backup that data on a regular basis.
Regularly review and update your backup strategy to ensure that it is in line with your evolving demands and the most recent best practices for data backup.
TIP #4- Take Caution When Using WiFi
Using public Wi-Fi exposes your online activities and sensitive information to possible attackers, who can intercept or manipulate your data, resulting in identity theft, financial loss, or other cybercrime. When using public Wi-Fi networks, it is critical to exercise caution and implement adequate security precautions.
Do not put your reliance in public Wi-Fi security.
Connecting to unprotected public Wi-Fi networks should be avoided.
Make sure your own Wi-Fi networks are password-protected.
Create a secure password for your Wi-Fi network and allow only authorized users access.
Change your wireless password on a regular basis.
TIP #5- Keep Software and Systems Up to Date
It's crucial to install software updates for your operating system and programs. Install the most recent security updates for your devices:
Maintaining your software and systems guarantees that you have the most recent security patches and fixes.
Install software updates as soon as possible, especially if they include crucial security changes.
Set your devices to receive automatic updates so you never miss one!
TIP #6- Be Cautious of links
Hackers frequently utilize links in emails to lure people into disclosing sensitive information. This frequently takes the guise of bank statements, flight tickets, password recovery emails, and other documents.
When a person clicks on one of these links, they are sent to a false site that appears suspiciously similar to the real thing. The site will prompt them to login or provide personal information. When a hacker obtains this information, they gain access to the user's account.
Avoid opening emails from unfamiliar or strange senders and clicking on suspicious links. They could contain malware or phishing scams.
Keep an eye out for links in your emails.
Don't click on anything that appears suspicious.
Rather than using an email, the best bet is to go directly to a provider's website.
TIP #7-Be Aware of Social Engineering Tactics
Social engineering is a technique used by online criminals/cyber attackers to trick people into disclosing private information or taking potentially dangerous actions. It entails the use of psychological manipulation techniques to trick, manipulate, or take advantage of people in order to access private data or systems.
Phishing, pretexting, baiting, and quid pro quo are examples of common social engineering techniques. Email, phone, social media, and in-person contacts are just a few of the communication methods that can be used for social engineering attacks.
TIP #8- Limit Personal Information Access
Be cautious when sharing personal information online, and limit the information you publish on social media and and other websites.
Avoid sharing sensitive information such as your full name, date of birth, home address, and phone number online.
Use a virtual private network (VPN) which encrypts your internet connection and hides your IP address, making it more difficult for others to track your online activities and access your personal information.
TIP #9- Use Antivirus Software
Malware, viruses, and other sorts of dangerous software can be detected and removed from your computer using antivirus software.
Install antivirus software on all of your computers and mobile devices, including laptops, desktops, cellphones, and tablets.
Maintain the antivirus software to the most recent version to ensure that it can identify and prevent the most recent threats.
Use trusted antivirus software from well-known vendors with a proven track record of detecting and stopping malware.
Disabling antivirus software, even briefly, leaves your device vulnerable to attacks.
Enable automatic updates so that the antivirus software can be updated with the most recent malware definitions.
Schedule frequent virus and malware scans for your device.
TIP #10- Educate Yourself
Keep up to date on the newest cybersecurity dangers and best practices for protecting yourself and your data online.
Read cybersecurity blogs to remain up to date on the newest threats and online safety tips.
Attend cybersecurity webinars to learn about particular cybersecurity subjects or issues.
Follow cybersecurity experts on social media to remain up to date on the newest cybersecurity news and trends.
Ignorance is an enemy, even to its owner. Knowledge is a friend, even to its hater. Ignorance hates knowledge because it is too pure. Knowledge fears ignorance because it is too sure.
Sri Chinmoy
These recommendations can assist you in protecting your personal information and digital assets from cyber threats.
1.4 Review Question
Which of the aforementioned cybersecurity safety measures have you overlooked or neglected to implement, if any?
Have you or a loved one been a victim of social engineering tactics? If so, what important lesson did you learn and how are you ensuring that you or your loved ones are no longer victims?